Pendoのデータプライバシーとセキュリティ
信頼獲得へのPendoのコミットメント
Pendoでは、パフォーマンス、セキュリティとプライバシーが最優先され、組織としてプロダクトやポリシーを設計する際の指針となっています。これらの原則は、私たちが行うすべての意思決定、そして企業としてのすべての行動の中心にあるべきものと考えています。そのため、私たちのソリューションがお客様のデータ、ユーザー、アプリケーションの整合性に悪影響を与えないよう徹底するために、これらの分野に多額の投資を続けています。
Pendoでは、パフォーマンス、セキュリティとプライバシーが最優先され、組織としてプロダクトやポリシーを設計する際の指針となっています。これらの原則は、私たちが行うすべての意思決定、そして企業としてのすべての行動の中心にあるべきものと考えています。そのため、私たちのソリューションがお客様のデータ、ユーザー、アプリケーションの整合性に悪影響を与えないよう徹底するために、これらの分野に多額の投資を続けています。
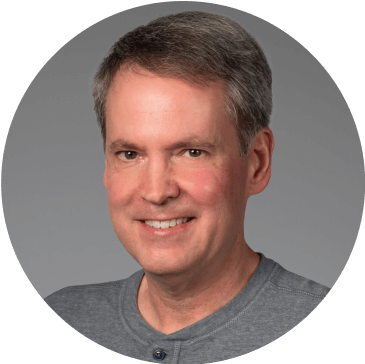
最高情報セキュリティ責任者 Chuck Keslerのご紹介
Keslerは10年以上にわたってセキュリティプログラムを主導し、Pendoが保護の責任を負うデータについて強力なコントロールを確保することに注力しています。
Keslerは10年以上にわたってセキュリティプログラムを主導し、Pendoが保護の責任を負うデータについて強力なコントロールを確保することに注力しています。
セキュリティへの投資
Pendoは、お客様のデータのセキュリティとプライバシーを保護するために、主要な業界のベストプラクティスと、SOC2、GDPR、TX-RAMP、HIPAAなどの規制スキームを遵守しています。
データ保護責任者
Pendoは、データプライバシーとセキュリティに関する全社横断的な提唱者として、データプライバシー責任者を任命しました。
プライバシーとセキュリティのトレーニング
Pendoの全従業員は、データプライバシーポリシーとベストプラクティスに関するトレーニングと認定を受けています。
ベンダー監査と承認プロセス
Pendoは、ライセンス供与、またはサードパーティのツールを使用する前に、幅広くコンプライアンスレビューを実施して、承認プロセスを通します。
データ暗号化とアクセスツール
送信時および保存時は、お客様のデータはすべて、業界で認められたデータ処理とセキュリティのツール、標準またはベストプラクティスのみを使用して暗号化しています。
役割ベースの権限
Pendoを使用すると、特定の役割と権限に基づいて機能を付与および制限するためのきめ細かいアクセス制御を設定できます。
監査証跡
Pendoは、監査と根本原因分析を容易にするために、すべての変更、すべてのアクション、およびデータの削除を含むすべてのイベントをログに記録して保存します。
データ削除リクエスト
Pendoでは、管理データと処理データの両方に対して、削除要求によるデータ削除が可能です。
データの分離とPII
顧客データは互いに論理的に分離されており、Pendoのプロダクト機能を最大限に活用するために個人を特定できる情報が必要になることはありません。
回復力とアップタイム
Pendoは、1時間に数百万、1日に数十億のイベントを処理してもパフォーマンスが低下しないよう、中断のないアップタイムとエンタープライズ規模向けの設計になっています。



Pendoのセキュリティ体制や関連文書に関する詳細は、TrustPageをご覧ください。
他にご質問がある場合
プライバシーおよびコンプライアンスに関するその他の情報については、プライバシーポリシーページをご覧いただくか、データプライバシーに関する具体的なご質問については[email protected]までお問い合わせください。
Pendoのセキュリティバグを発見し、ご報告いただける場合は、[email protected]までメールでご連絡ください。
プライバシーおよびコンプライアンスに関するその他の情報については、プライバシーポリシーページをご覧いただくか、データプライバシーに関する具体的なご質問については[email protected]までお問い合わせください。
Pendoのセキュリティバグを発見し、ご報告いただける場合は、[email protected]までメールでご連絡ください。